In the world of networking, ports play a crucial role in facilitating communication between devices. They act as virtual doors through which data enters and exits a device or network. However, not all ports are open and available for use. Some may be “closed,” meaning no service is actively using them, while others may be “filtered,” meaning they are intentionally blocked or restricted by security measures, like firewalls.
Understanding the difference between these two states—closed and filtered—is essential for anyone involved in networking or troubleshooting connectivity issues. A closed port may simply be unavailable for communication, while a filtered port could indicate a security measure that’s preventing access, even though the port itself may technically exist.
Knowing whether a port is closed or filtered can help in diagnosing network problems, ensuring the correct configuration of network services, and maintaining the security of your devices. In this article, we will explore the definitions, causes, and implications of closed and filtered ports, and how to resolve issues related to them.
What is a Port in Networking?
In networking, a port is a logical endpoint used for communication between devices over a network. It is a part of the internet protocol (IP) address that helps direct network traffic to specific processes or services running on a computer or server.
Key Concepts:
Ports as Communication Channels:
A port acts as a channel or doorway through which data is sent and received between devices. Each port is associated with a specific number, and different applications or services use different port numbers to ensure data reaches the correct destination.
IP Address + Port Number:
A port works together with an IP address to create a unique endpoint for data transmission. For example, when you connect to a website, your computer communicates with the server using the server’s IP address and a specific port number (usually port 80 for HTTP or port 443 for HTTPS).
Example:
IP address: 192.168.1.1
Port number: 80 (for HTTP)
The combination of the IP address and port number forms the complete “address” for a specific service on a device, which can be thought of as a “network socket.”
Types of Ports:
Ports can be categorized into well-known ports, registered ports, and dynamic or private ports.
Well-Known Ports (0-1023):
These are used by essential services and protocols. For example, port 80 is used by HTTP (web browsing), and port 443 is used by HTTPS (secure web browsing).
Registered Ports (1024-49151):
These are used by software applications that are not part of the operating system but require specific ports for communication (e.g., certain database services, game servers).
Dynamic or Private Ports (49152-65535):
These are used temporarily for client-side communication when initiating a connection with a server. These ports are dynamically assigned for each session and are not typically used by specific services.
TCP vs. UDP Ports:
Ports are used in both TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) connections, which are the two main transport layer protocols.
TCP Ports are used for reliable, connection-oriented communication (e.g., web browsing, file transfers).
UDP Ports are used for faster, connectionless communication (e.g., streaming, gaming).
How Ports Work in Networking:
When a device wants to communicate over the internet or a local network, it uses the port number to identify which process or service should handle the incoming or outgoing data. For example, a computer requesting a webpage sends the request to port 80 on the web server. The server receives the request through that port, processes it, and sends back the web page data.
Port Numbering:
Port Range: Ports are numbered from 0 to 65535.
Ports 0-1023 are known as well-known ports, commonly used for standard services (e.g., HTTP, FTP, SSH).
Ports 1024-49151 are registered ports, used by applications and software.
Ports 49152-65535 are dynamic or private ports, often used temporarily by clients when communicating with servers.
Importance of Ports:
Service Identification: Ports help identify which service should handle a request. For instance, if you are accessing a website, port 80 (HTTP) or 443 (HTTPS) will be used to load the page.
Network Communication: Ports are essential for any network communication, whether it’s between servers, computers, or devices in a network.
Security: Open ports can be security risks if they are not properly managed. Attackers may try to exploit vulnerabilities in certain services that use open ports, so it’s crucial to monitor and control which ports are open.
Example of Port Use:
When you visit a website:
Your browser sends a request to the server’s IP address using port 80 (for HTTP).
The server processes the request and sends back the data through the same port.
Your browser then displays the website.
Without ports, it would be impossible to direct network traffic to the correct services and applications running on a device.
A port in networking is a number assigned to specific network services or applications that helps route network traffic to the correct process on a device. It plays a crucial role in enabling effective communication between devices on a network.
Understanding Port Status
When dealing with networks and communication between devices, it’s essential to understand the status of a port. A port in networking acts like a doorway through which data enters and exits a device. Ports are used to enable different services and applications (e.g., websites, email servers, file transfer services) to communicate across a network.
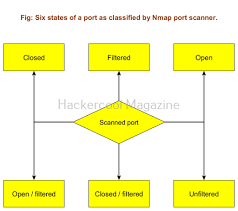
The status of a port helps determine how it behaves during these communications. The most common port statuses you’ll encounter are open, closed, and filtered. Understanding these statuses is crucial for network troubleshooting and security.
1.Open Port
Definition: An open port is one that is actively accepting incoming connections. When a port is open, it means that a service or application on your device is listening for traffic on that port.
Why it’s important:
An open port signifies that a specific service, like a web server (port 80) or a game server, is running and accessible to the network or the internet.
For example, if you’re hosting a website, port 80 (HTTP) must be open to allow users to access your site.
How it’s used:
When an open port is contacted by another device over the network (via its IP address and specific port number), it will respond, allowing data to be transferred between the devices.
Open ports are essential for any type of service that needs to be accessed remotely (e.g., online games, web hosting, remote desktop).
2.Closed Port
Definition: A closed port is one where no application is currently listening for connections. Essentially, it’s like a closed door—if a request comes to that port, it won’t receive any response from the device.
Why it’s important:
A closed port doesn’t mean that the port is necessarily secure. It simply means no program or service is actively using it.
In many cases, a closed port means that there’s no need for external traffic to be sent to that port, so it’s not open to outside access.
How it’s used:
A port may be closed if no program is assigned to listen on that port, or if a firewall is configured to block incoming connections on it.
Sometimes, a port that is closed may not respond to external connection attempts, resulting in timeouts or errors.
3.Filtered Port
Definition: A filtered port is a port where incoming traffic is blocked or filtered by a firewall, router, or other network security device. This makes it appear as though the port is closed, even if a service might be listening on it.
Why it’s important:
A filtered port appears to be unresponsive or “closed” to external devices, but the reason for this is that a firewall or network security device is blocking the connection, not because there’s no service running.
Filtered ports are common when firewalls or security policies are configured to block certain types of incoming traffic.
How it’s used:
For example, if a firewall is set to block all incoming connections on port 25 (commonly used for email servers), the port would be reported as “filtered,” making it seem like the port is closed when, in fact, it’s being deliberately blocked by security measures.
Filtered ports are often used to increase security by preventing unauthorized or malicious access to specific services or devices.
What Does it Mean When a Port is Closed?
A closed port refers to a port on a network device (such as a computer, server, or router) that is not currently accepting incoming connections. In simpler terms, when a port is closed, there is no service actively listening for or responding to requests made to that port.
Understanding Ports:
Before diving into what it means for a port to be closed, it’s essential to understand what a port is. In networking, a port is a virtual endpoint for communication, allowing different types of network traffic (such as web traffic, email, or file sharing) to be directed to the correct application or service on a device. Each port is identified by a number, and these numbers are grouped into categories (well-known ports, registered ports, dynamic/private ports).
Why Are Ports Closed?
No Application Running on the Port: A port may be closed because there is no application or service listening for incoming traffic on that port. For example, if you have a web server running on port 80 (HTTP) and no server is running on port 21 (FTP), port 21 will remain closed. In this case, when someone tries to connect to that port, they will receive no response.
Intentional Network Configuration: Ports may be closed intentionally by network administrators to enhance security. Closing unnecessary ports reduces the attack surface, preventing malicious actors from exploiting open ports for unauthorized access. For example, if a port is not needed for any service, it may be closed to prevent unwanted traffic from reaching the device.
Firewall or Router Configuration: Firewalls or routers may block certain ports as part of network security policies. A firewall might be set to close specific ports for inbound or outbound traffic, even if the service on the device would otherwise be listening on those ports.
Connection Refused by the Device: Sometimes, the device may be set to actively reject connections on a certain port. This could happen due to a policy, misconfiguration, or overload of the system, where the device doesn’t allow connections to that port.
How Does It Differ from an Open Port?
An open port is one that is actively listening for incoming traffic and can establish a connection with a requesting device. Services like web servers (HTTP on port 80), email servers (SMTP on port 25), or game servers typically use open ports to interact with clients.
A closed port, on the other hand, means that there is no application currently bound to that port, so it won’t respond to connection attempts.
In many cases, a closed port is simply a port that is not being used. Unlike an open port, a closed port won’t allow you to access any service.
What Happens When You Try to Access a Closed Port?
When you attempt to connect to a closed port, one of the following can happen:
Connection Timeout: The connection attempt will time out after waiting for a response that never comes because there is no service listening on that port.
Connection Refused: If the device or firewall is configured to reject connections, you might see a “connection refused” message, indicating that the server is reachable, but it is intentionally not allowing the connection on that specific port.
Real-World Example:
Imagine you are trying to access a website hosted on a server. If the website is using HTTP (port 80), your computer will try to connect to port 80 on the server’s IP address. If port 80 is closed, the request won’t be answered, and you won’t be able to access the website.
How to Check if a Port is Closed:
Using a Port Checker Tool: Online port checkers or port scanning tools (like YouGetSignal or CanYouSeeMe) allow you to check whether a particular port is open or closed. These tools send a request to the port on your device and wait for a response.
Command Line Tools: On your own device, you can use tools like netstat (Windows/Linux) or telnet to see if a service is listening on a particular port. For example, running telnet will try to establish a connection to the specified IP and port.
Why is it Important to Know if a Port is Closed?
Security: Knowing which ports are closed helps you secure your device or network by ensuring that no unnecessary ports are left open, reducing the potential for cyberattacks.
Network Troubleshooting: If a service isn’t accessible, it might be because the port it’s supposed to listen on is closed. By checking the port status, you can diagnose and resolve connectivity issues.
Service Availability: Some applications or services require specific ports to be open for proper functioning. If a necessary port is closed, the service may fail to work as expected.
How to Determine if a Port is Closed or Filtered?
Determining whether a port is closed or filtered involves testing the connection and analyzing the response from the network. Here’s a breakdown of how to determine whether a port is closed or filtered:
1.Understanding the Key Differences Between Closed and Filtered Ports
Before testing, it’s important to understand the distinction:
Closed Port: A port is considered closed if there is no service listening on that port. When you try to connect to it, you may receive a “connection refused” or similar error, indicating that no application is handling the request.
Filtered Port: A port is considered filtered if it is being blocked by a firewall, router, or network policy. The device doesn’t respond to the connection attempt, often causing the request to “time out” or appear to be unreachable. The connection attempt is silently dropped, as if the port does not exist.
2.Tools to Check Port Status
There are several methods and tools available to check whether a port is closed or filtered:
a.Online Port Checkers
These web-based tools allow you to test whether a port is open, closed, or filtered from an external perspective (outside your network). Some examples of these tools include:
YouGetSignal: Tests your public IP address and checks whether a specific port is open.
CanYouSeeMe: Checks if a port is accessible from the outside world.
PortChecker.co: Another simple online tool for port testing.
To use an online port checker:
- Enter the port number you want to test.
- The tool will attempt to access your IP address on that port.
- If the port is open, it will show a “success” message. If it’s closed, it will say “connection refused,” and if it’s filtered, it may report a timeout or no response.
b.Command-Line Tools (for Local Testing)
Telnet (Windows/macOS/Linux): Telnet is a command-line tool that can be used to test connections to specific ports.
Example: telnet your-ip-address port-number
If the connection is successful, the port is open. If you get a “connection refused” message, the port is closed. If there’s no response or a timeout, the port is likely filtered.
Netcat (nc) (Linux/macOS): Netcat is similar to Telnet but offers more flexibility.
Example: nc -zv your-ip-address port-number
This command checks if the port is open or closed. A filtered port will show a timeout or no response.
c.Port Scanning Tools
Advanced users or administrators often use port scanning tools that provide detailed reports on open, closed, and filtered ports on a network:
Nmap: One of the most popular port scanning tools, Nmap can detect open, closed, and filtered ports. It also helps identify which services are running on those ports.
Example Command: nmap -p port-number your-ip-address
The results will display whether the port is open, closed, or filtered.
Zenmap: The graphical version of Nmap, which is easier to use for beginners.
3.Interpreting the Results
Open Port: If the connection is successful, the port is open. This means that an application is actively listening for incoming connections on that port.
Closed Port: If the port is closed, you will typically see one of these responses:
Connection Refused: This means the port is closed, and no service is listening on that port.
Connection Reset: Some tools might show this if the port is closed or filtered but actively rejecting connections.
Filtered Port: If the port is filtered, the following behaviors can occur:
Timeout: The connection attempt to the port takes too long and eventually times out, suggesting that the port is being blocked by a firewall or router.
No Response: The tool may not get any response from the port, indicating that it is filtered.
In many cases, when a port is filtered, the response is subtle: there’s no indication that the port is there, leading you to believe that it’s not open at all. This is different from a closed port, where you at least know that something exists but is actively refusing connections.
4.Using Firewalls or Router Settings to Detect Filtering
In some cases, the results of a test may indicate that a port is filtered, but the firewall or router is configured to block specific types of traffic. To check if filtering is happening locally:
Temporarily Disable Firewalls: Disable your firewall temporarily and check the port again to see if it is still filtered.
Check Router Port Forwarding Settings: Ensure that port forwarding rules are configured properly. If a router is filtering traffic, you might need to adjust the settings to allow inbound connections on the desired port
5.Other Possible Causes of Filtered Ports
ISP Blocking: Some ISPs block specific ports for security or network management reasons. This might explain why certain ports appear filtered even though your firewall or router settings are correct.
Network Address Translation (NAT) Issues: If you’re behind a NAT router, the external IP address you’re using might not match the internal device configuration, leading to filtering or misconfiguration.
How to Resolve Issues with Closed or Filtered Ports
When you encounter closed or filtered ports, it can prevent you from accessing necessary services or applications (like gaming servers, web hosting, or remote work tools). Understanding how to resolve these issues is crucial for ensuring smooth network operations and maintaining a secure network. Here’s a breakdown of how to address both closed and filtered ports.
1.Resolving Closed Ports
A closed port occurs when there is no active service or application listening on that port, or when the port is intentionally blocked by the firewall. Here’s how to resolve closed port issues:
Step-by-Step Guide for Closed Ports:
Check if the Associated Service is Running:
Ensure that the application or service that should be listening on the port is actually running. For example, if you’re trying to access a web server on port 80, make sure the web server software (like Apache or Nginx) is up and running.
Windows: Use Task Manager or the services.msc tool to verify that the service is running.
Linux: Use ps aux | grep or check with systemctl status .
Verify Port Forwarding Settings:
If you’re behind a router (NAT), make sure that the router is forwarding the correct port to your internal machine. You can usually do this by logging into your router’s settings and checking the port forwarding section.
Example: If you’re running a game server on port 25565, make sure the router forwards external requests on port 25565 to the correct internal IP address and port.
Check Firewall Settings:
On both the router and the local machine, firewalls may be blocking the port. Verify that the firewall is allowing traffic through the required port.
Windows: Go to Control Panel > Windows Defender Firewall and add an inbound rule for the required port.
Linux: Use iptables or ufw to allow the port (e.g., sudo ufw allow 8080/tcp).
Check for ISP Blockages:
In some cases, your Internet Service Provider (ISP) may block certain ports (like port 25 for email). If you’re unable to open a port, it’s worth checking with your ISP to see if they are blocking it.
You can use online port checkers to confirm whether the ISP is blocking the port, and contact the ISP if necessary.
2.Resolving Filtered Ports
A filtered port occurs when traffic to the port is being blocked or redirected, typically by a firewall, router, or ISP filter. Here’s how to resolve issues with filtered ports:
Step-by-Step Guide for Filtered Ports:
Check the Router’s Firewall or Security Settings:
Many routers have built-in firewalls that may filter incoming or outgoing traffic on certain ports. Log into your router’s admin panel and review the security or firewall settings to ensure the port you need is not being filtered or blocked.
Look for any “Access Control” or “Traffic Filtering” settings and check if the port is being restricted.
Modify or Disable Local Firewalls:
Local firewalls on your computer or device may be filtering the port. If you’re using a firewall (e.g., Windows Firewall, third-party firewall software), ensure that the specific port is allowed.
Windows: In Windows Defender Firewall, add an inbound or outbound rule to permit traffic on the filtered port.
Mac/Linux: Modify firewall settings using built-in tools like iptables (Linux) or pf (Mac).
Bypass the Filter with VPN or Proxy:
If the port is being filtered by your ISP, you may be able to bypass the filter using a VPN (Virtual Private Network) or proxy server. A VPN encrypts your traffic and routes it through a different server, potentially bypassing any network filtering or restrictions imposed by your ISP.
Choose a VPN service with reliable server locations and configure it to route your traffic over an unblocked port or a different server.
Configure the Firewall for Specific Applications:
Ensure that the firewall allows the specific application to communicate through the filtered port. Some firewalls may have settings to allow only specific types of traffic (e.g., HTTP/HTTPS, FTP), so check that the app you’re using is configured to bypass the firewall filtering.
Contact Your ISP or Network Administrator:
If the filtered port is being blocked at the ISP or corporate network level, you may need to contact them directly to resolve the issue. Some ISPs block ports to prevent abuse or security threats, and they might be able to lift the restriction upon request.
In corporate networks, the network administrator may have implemented security policies that block certain ports; discussing the issue with them can help.
3.General Best Practices for Resolving Port Issues
Regular Port Audits: Periodically check which ports are open or filtered on your network. This can help identify potential security risks or misconfigurations early.
Minimize Open Ports: Only keep the ports open that are necessary for your services or applications. Every unnecessary open port can increase security vulnerabilities.
Keep Software Updated: Ensure that all services and applications listening on open ports are kept up to date with the latest patches to protect against vulnerabilities.
Use Secure Methods (e.g., HTTPS, SSH): If you need to expose services like web servers or remote access, ensure that you use secure protocols (e.g., HTTPS instead of HTTP, SSH instead of Telnet) to protect your data.
How to Resolve Issues with Closed or Filtered Ports
When you encounter closed or filtered ports, it can prevent you from accessing necessary services or applications (like gaming servers, web hosting, or remote work tools). Understanding how to resolve these issues is crucial for ensuring smooth network operations and maintaining a secure network. Here’s a breakdown of how to address both closed and filtered ports.
1.Resolving Closed Ports
A closed port occurs when there is no active service or application listening on that port, or when the port is intentionally blocked by the firewall. Here’s how to resolve closed port issues:
Step-by-Step Guide for Closed Ports:
Check if the Associated Service is Running:
Ensure that the application or service that should be listening on the port is actually running. For example, if you’re trying to access a web server on port 80, make sure the web server software (like Apache or Nginx) is up and running.
Windows: Use Task Manager or the services.msc tool to verify that the service is running.
Linux: Use ps aux | grep or check with systemctl status .
Verify Port Forwarding Settings:
If you’re behind a router (NAT), make sure that the router is forwarding the correct port to your internal machine. You can usually do this by logging into your router’s settings and checking the port forwarding section.
Example: If you’re running a game server on port 25565, make sure the router forwards external requests on port 25565 to the correct internal IP address and port.
Check Firewall Settings:
On both the router and the local machine, firewalls may be blocking the port. Verify that the firewall is allowing traffic through the required port.
Windows: Go to Control Panel > Windows Defender Firewall and add an inbound rule for the required port.
Linux: Use iptables or ufw to allow the port (e.g., sudo ufw allow 8080/tcp).
Check for ISP Blockages:
In some cases, your Internet Service Provider (ISP) may block certain ports (like port 25 for email). If you’re unable to open a port, it’s worth checking with your ISP to see if they are blocking it.
You can use online port checkers to confirm whether the ISP is blocking the port, and contact the ISP if necessary.
2.Resolving Filtered Ports
A filtered port occurs when traffic to the port is being blocked or redirected, typically by a firewall, router, or ISP filter. Here’s how to resolve issues with filtered ports:
Step-by-Step Guide for Filtered Ports:
Check the Router’s Firewall or Security Settings:
Many routers have built-in firewalls that may filter incoming or outgoing traffic on certain ports. Log into your router’s admin panel and review the security or firewall settings to ensure the port you need is not being filtered or blocked.
Look for any “Access Control” or “Traffic Filtering” settings and check if the port is being restricted.
Modify or Disable Local Firewalls:
Local firewalls on your computer or device may be filtering the port. If you’re using a firewall (e.g., Windows Firewall, third-party firewall software), ensure that the specific port is allowed.
Windows: In Windows Defender Firewall, add an inbound or outbound rule to permit traffic on the filtered port.
Mac/Linux: Modify firewall settings using built-in tools like iptables (Linux) or pf (Mac).
Bypass the Filter with VPN or Proxy:
If the port is being filtered by your ISP, you may be able to bypass the filter using a VPN (Virtual Private Network) or proxy server. A VPN encrypts your traffic and routes it through a different server, potentially bypassing any network filtering or restrictions imposed by your ISP.
Choose a VPN service with reliable server locations and configure it to route your traffic over an unblocked port or a different server.
Configure the Firewall for Specific Applications:
Ensure that the firewall allows the specific application to communicate through the filtered port. Some firewalls may have settings to allow only specific types of traffic (e.g., HTTP/HTTPS, FTP), so check that the app you’re using is configured to bypass the firewall filtering.
Contact Your ISP or Network Administrator:
If the filtered port is being blocked at the ISP or corporate network level, you may need to contact them directly to resolve the issue. Some ISPs block ports to prevent abuse or security threats, and they might be able to lift the restriction upon request.
In corporate networks, the network administrator may have implemented security policies that block certain ports; discussing the issue with them can help.
3.General Best Practices for Resolving Port Issues
Regular Port Audits: Periodically check which ports are open or filtered on your network. This can help identify potential security risks or misconfigurations early.
Minimize Open Ports: Only keep the ports open that are necessary for your services or applications. Every unnecessary open port can increase security vulnerabilities.
Keep Software Updated: Ensure that all services and applications listening on open ports are kept up to date with the latest patches to protect against vulnerabilities.
Use Secure Methods (e.g., HTTPS, SSH): If you need to expose services like web servers or remote access, ensure that you use secure protocols (e.g., HTTPS instead of HTTP, SSH instead of Telnet) to protect your data.
Best Practices for Port Management
Port management is crucial for maintaining a secure and efficient network. Open ports can expose systems to security risks, while properly configured ports can help ensure that applications and services work correctly. Below are some of the best practices for managing ports in a network:
1.Minimize Open Ports
Keep Only Necessary Ports Open:
Only open ports that are needed for specific services or applications. Unnecessary open ports should be closed to reduce the attack surface for potential intruders.
Default Ports:
Avoid using default ports for critical services (e.g., HTTP on port 80). Attackers are often aware of these default ports and may target them. Consider using non-standard ports for better security.
2.Regularly Review and Audit Open Ports
Periodic Audits:
Regularly check which ports are open on your devices, servers, and routers. Over time, network configurations can change, and previously open ports might no longer be necessary.
Automated Tools:
Use port scanning tools (like Nmap, OpenVAS, or online port checkers) to automate the auditing process. These tools can help identify unexpected open ports or vulnerable services.
3.Secure Communication on Open Ports
Use Encryption:
When using open ports for communication, ensure that traffic is encrypted, particularly for sensitive data. For instance, use HTTPS (port 443) instead of HTTP (port 80) to secure web traffic, and consider SSH (port 22) for remote access rather than unencrypted protocols like Telnet.
Firewall Rules:
Configure firewalls to allow traffic only from trusted IP addresses or subnets on open ports. For example, restrict access to administrative ports (like SSH) to known IP addresses to prevent unauthorized login attempts.
4.Implement Proper Firewall Configuration
Use a Stateful Firewall:
A stateful firewall can track the state of active connections and make dynamic decisions based on this state. For example, it can allow incoming packets from a certain IP address only if there is already an established connection.
Block Unused Ports:
Configure your firewall to block all ports by default and only allow traffic on ports required for your services. This practice helps prevent unauthorized access.
5.Use Port Forwarding Carefully
Limit Port Forwarding:
Port forwarding allows external devices to connect to internal services, but it can introduce security risks if not carefully managed. Only forward ports for services that need external access, and ensure these services are secured with strong authentication and encryption.
Reverse Proxies for Internal Services:
Instead of directly forwarding ports to internal services, use a reverse proxy to act as an intermediary. This can hide internal server details from the outside world and add an extra layer of security.
6.Apply Network Segmentation
Separate Sensitive Networks:
For larger organizations or those with sensitive data, segment your network into subnets. This limits the scope of open ports to specific network segments, reducing the risk of lateral movement in case of a breach.
Demilitarized Zone (DMZ):
Consider using a DMZ to place publicly accessible services (e.g., web servers, email servers) in an isolated segment of your network. This helps protect internal systems from external threats.
7.Monitor and Detect Unusual Port Activity
Intrusion Detection Systems (IDS):
Deploy IDS to monitor traffic for signs of suspicious activity, such as unauthorized attempts to access open ports. Many IDS systems can alert you when specific ports are being targeted by attackers.
Traffic Analysis:
Regularly analyze traffic patterns for unusual port access. For example, if a port that is usually not in use suddenly receives traffic, it may indicate an attempt to exploit a vulnerability.
8.Close Inactive or Unused Ports
Turn Off Services You Don’t Use:
If a service that uses a particular port is no longer needed, stop the service and close the port. This helps prevent unnecessary exposure.
Disable Default Services:
Many devices and systems come with default services (such as FTP or Telnet) that are rarely needed. Disable or remove these services to reduce the number of open ports.
9.Apply Security Patches and Updates
Keep Software Updated:
Vulnerabilities in software or hardware can be exploited through open ports. Ensure that all systems, especially those with open ports, are kept up to date with security patches to prevent known exploits.
Automate Security Updates:
Set up automatic security updates whenever possible to keep your system protected from newly discovered vulnerabilities.
10.Use VPNs for Remote Access
Secure Remote Access:
Instead of opening ports for remote services (such as remote desktop), use a Virtual Private Network (VPN) to encrypt and secure connections. VPNs create a secure tunnel that can protect data and limit exposure to open ports.
Limit VPN Access:
Only grant VPN access to trusted users, and make sure the VPN is protected with strong authentication methods like two-factor authentication (2FA).
Conclusion
A closed port means no service is listening on that port, and it’s not accepting connections, which is generally safe but can affect functionality. A filtered port, on the other hand, is blocked by a firewall or network device, making it appear closed but actively preventing access. Understanding these differences helps in troubleshooting and securing your network. Regularly checking port statuses and configuring firewalls properly is essential for maintaining both security and service functionality.